Deepfake: attack on trust as a new standard
A dangerous trend for crypto fraud
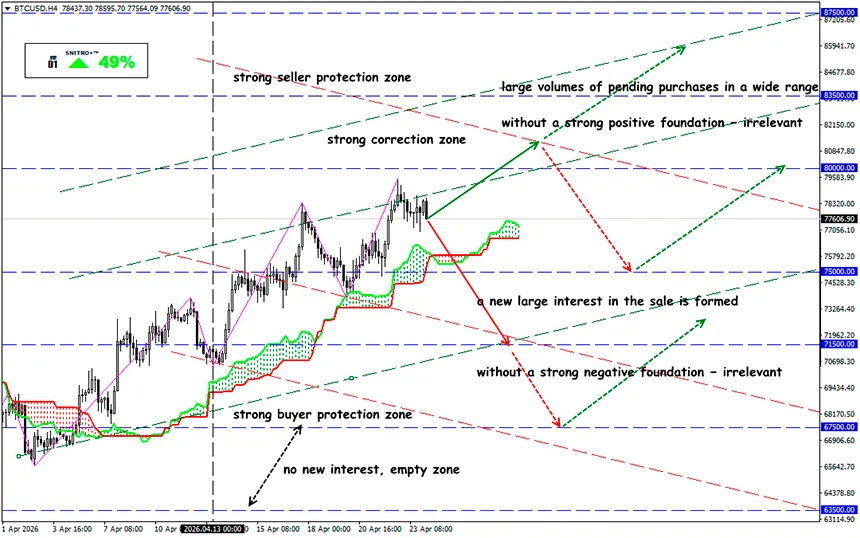
BTC/USD
Key zone: 76,800 - 78,500
Buy: 78,200 (on a strong positive foundation); target 81,500-83,500; StopLoss 77,200
Sell: 76,500 (after retesting 77,200) ; target 73,500; StopLoss 77,500
2026 has become a turning point for cybersecurity in the crypto market: deepfake technologies have evolved from a tool of marketing scams into a full-fledged weapon. While in 2023–2024 the main threat came from smart contract exploits, there is now a clear shift toward identity-layer attacks — compromising trust through “synthetic” virtual identities.
According to Cointelegraph, since the beginning of 2026 the crypto industry has already lost more than $600 million due to hacks. Among them are the $293 million Kelp DAO exploit on April 17 caused by a single point of trust in the LayerZero cross-chain infrastructure, as well as the $280 million Drift Protocol hack. The cost of attacks is decreasing — AI scams have increased by 456% over the year.
Recall:
Deepfake videos began developing in the late 2010s — the first neural network-based algorithms capable of generating realistic images appeared. By the early 2020s, deepfakes moved beyond experiments: generation quality improved, entry barriers decreased, and video editing software became accessible to a wide audience.
Deepfake fraud has already scaled to an “industrial level,” and the entry barrier has been almost eliminated. Factors that simplify hacking:
- irreversibility of transactions;
- high concentration of crypto liquidity;
- decentralized governance (DAO, multisig);
- active use of remote communications (Zoom, Telegram, Discord).
Deepfake integrates perfectly into this scheme: it attacks the level of human trust rather than program code. This is a hack of a “synthetic identity,” where the deepfake becomes the entry point into the information supply chain.
Unlike standard banking compliance, crypto lacks strict verification procedures, decisions are made quickly (especially in trading and OTC), and fraudulent schemes can be promoted via QR codes. Currently, mass deepfake scams are conducted through media and streaming, such as fake NVIDIA GTC streams or deepfake Elon Musk appearances, fake interviews, and fabricated kompromat on competitors. As a result, KYC/AML restrictions can be bypassed, access to custodial systems can be obtained, and infiltration into teams (insider threat) becomes possible.
Traditional protection methods, such as 2FA, do not work. The next stage is full automation of deepfake attacks via AI agents, which will further increase the frequency and scale of hacks.
One of the most illustrative incidents is linked to North Korean group UNC1069 using Deepfake Zoom attacks:
- the victim receives a Zoom invitation from a “partner”;
- the interface is spoofed (fake Zoom);
- a deepfake video is activated;
- “technical issues” are simulated;
- the victim is persuaded to execute commands, granting access.
Result:
- account compromise;
- theft of private keys and access credentials;
- subsequent withdrawal of funds.
Such attacks are systematically used to steal funds from crypto companies.
What is the result?
Information processes must be redesigned so that deepfake cannot become a decision-making point.
- Zero-trust communications — any financial actions are executed only via out-of-band confirmation.
- Digital multisignature — only with independent channels (different devices, different networks).
- Use deepfake artifact analysis via AI detectors.
- Minimize public data, control team digital communication.
- Reject trust in multimedia content as a confirmation factor.
- Mandatory cryptographic verification of actions.
- Any “urgent” action must be confirmed by at least two independent participants.
- Prohibition on software installation during multimedia contact.
It is important to understand that deepfake attacks target not protocols but processes, and they undermine the fundamental model of the crypto market: the principle “don’t trust, verify” becomes technically harder to implement. The most vulnerable points: OTC deals, DAO governance (influence on voting), access to funds via fake founders, and transaction confirmations.
Remember: even the most perfect smart contract will not protect against human error. But соблюдение multi-factor security requirements can preserve your funds.
So we act wisely and avoid unnecessary risks.
Profits to y’all!
























